What’s New in Progress Automate MFT: February 2026
February 03, 2026
See how Progress Automate MFT can now help your file-based workflows with simpler integration and more resilient automation.
Why Healthcare Organizations Are Moving Secure File Transfer to the Cloud
In HIPAA-regulated environments, even minor lapses could have serious consequences. Compliance-ready cloud file transfer software could help.
Simplify the Stack, Amplify the Story: Suzanne Reed on Human-Centered Marketing & Integrated Growth
ICYMI: Suzanne Reed on reclaiming strategy, streamlining martech and keeping marketing human.
Content Velocity vs. Content Debt: The Real Math Behind Publishing Speed
It’s time to figure out the cost of maintaining the content your team is pressured to keep producing. Velocity isn’t as important as value.
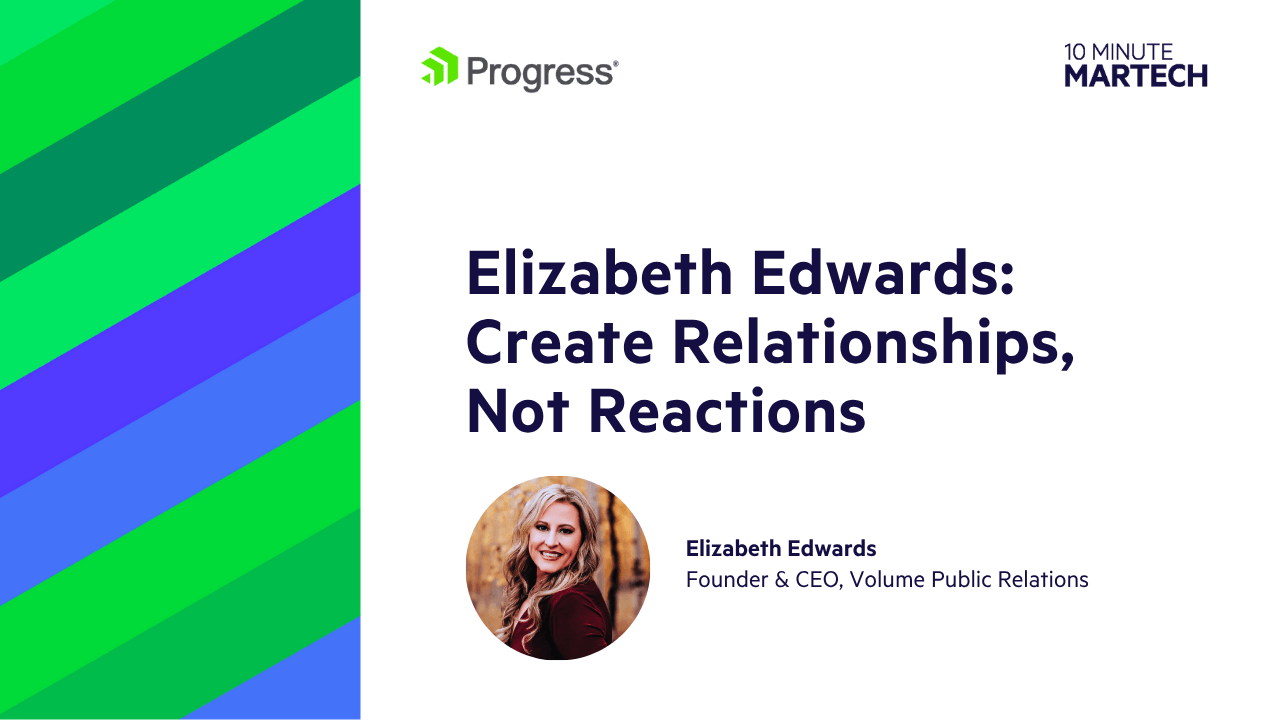
Elizabeth Edwards on Trust, Language & the Limits of AI Persuasion
ICYMI: Elizabeth Edwards talks affective science, ethical marketing and why credibility is the new growth lever.
Also Able to Explore

Latest Stories in Your Inbox
Subscribe to get all the news, info and tutorials you need to build better business apps and sites