External Authentication and FIPS Compliance with Hybrid Data Pipeline

New security enhancements to Hybrid Data Pipeline include external authentication over OAuth, LDAP, Okta and more, plus FIPS support for federal compliance.
Hybrid Data Pipeline, the groundbreaking data access service from DataDirect, recently released several new features to meet market demand and remain on the cutting edge of data services. Security requirements are in higher demand than ever before, and Hybrid Data Pipeline continues to be at the forefront of data security.
What is Hybrid Data Pipeline?
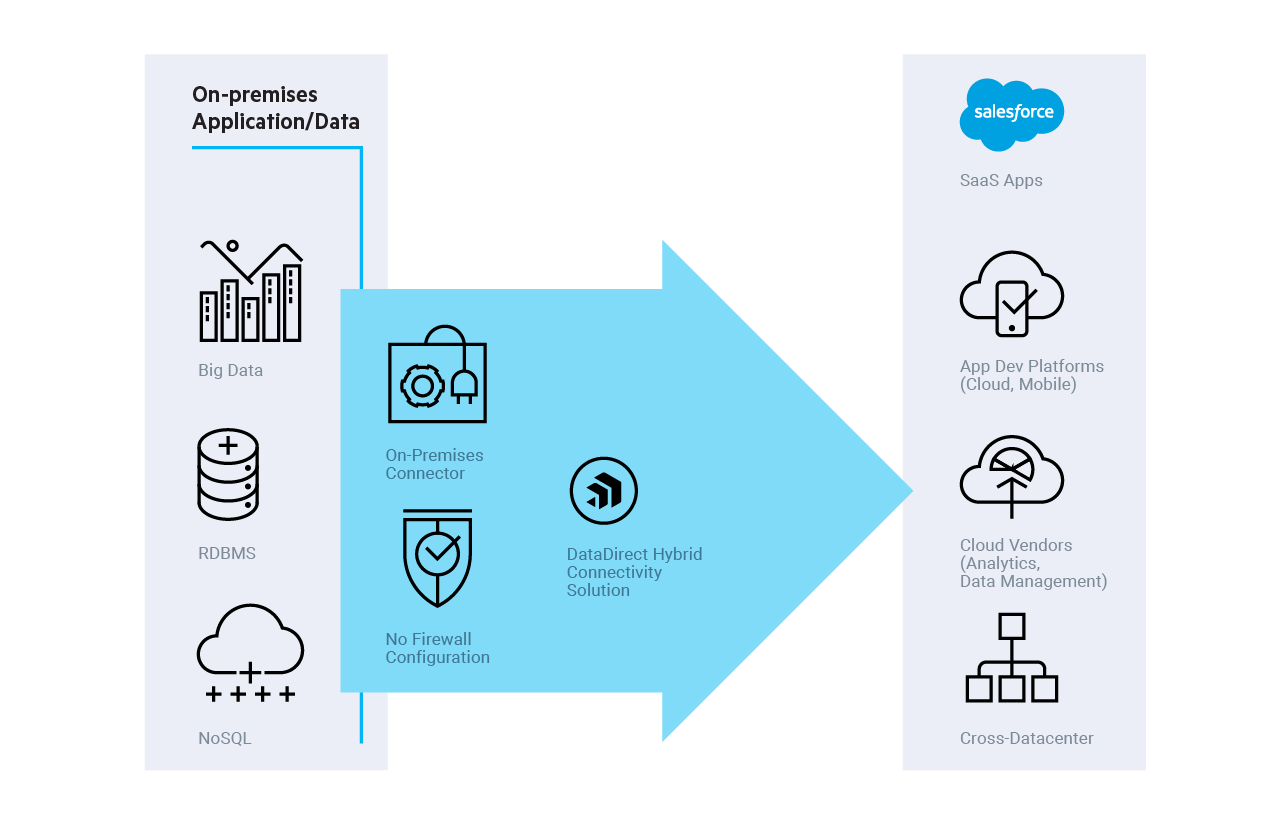
Hybrid Data Pipeline is a lightweight, embeddable data access service that simplifies integration by connecting directly to the data. This enables applications to use SQL or OData to perform real-time access to on-premises and cloud data. This prevents developers from having to do ETL. Connecting directly to the data in real-time is more agile than setting up a middle tier and is better than ETL for several use cases.
What's New in Hybrid Data Pipeline?
- External Authentication Support: In addition to its internal authentication, Hybrid Data Pipeline now supports external authentication methodologies, such as LDAP, OAuth and Okta, via Java plugin. External authentication allows administrators to call their existing systems of authentication through APIs, for an added layer of security. Users also have the ability to write Java code to handle authentication in a way that best fits their environment. This authentication system also adds a layer of flexibility to Hybrid Data Pipeline, as administrators can choose to map multiple externally authenticated users to a single Hybrid Data Pipeline user to more easily control data source access.
- FIPS Compliance: Hybrid Data Pipeline Server now provides a configuration where it can be run in FIPS 140-2 compliant mode. FIPS, the Federal Information Processing Standard, is a cryptography standard defining security compliance for both hardware and software. Why is FIPS important? Compliance means that software has met the security standards for deployment by U.S. federal agencies and federal contractors. In addition, FIPS is an established standard for security industry-wide since it is accredited by both the US and Canadian governments.
- FedRAMP Account Lockout Policy: Hybrid Data Pipeline supports the implementation of an account lockout policy, which can be used to limit the number of consecutive failed authentication attempts permitted before a user account is locked. The user is unable to authenticate until a configurable period of time has passed or until the administrator unlocks the account. The Hybrid Data Pipeline account lockout policy is by default enabled in accordance with Federal Risk and Authorization Management Program (FedRAMP) low- and medium-risk guidelines. FedRAMP Account Lockout Policy and FIPS compliance together make Hybrid Data Pipeline easy to use for Federal customers.
Security Policy
Progress DataDirect is committed to providing secure data access to its customers. Upon identification of any security vulnerability that would impact one or more Progress product(s), Progress will exercise commercially reasonable efforts to address the vulnerability in accordance with the following guidelines:
Security Vulnerability Response Policy
|
PRIORITY* |
TIME GUIDELINE |
VERSION(S) |
|
High Risk |
30 days |
Active (i.e. latest shipping version) and all Supported versions |
|
Medium Risk |
180 days |
Active (i.e. latest shipping version) |
|
Low Risk |
Next major release or best effort |
Active (i.e. latest shipping version) |
* Priority is established based on the current version of the Common Vulnerability Scoring System (CVSS), an open industry standard for assessing the severity of computer system security vulnerabilities. For additional information on this scoring system, refer to this page.
How are Companies Using Hybrid Data Pipeline?
Progress partners are using the Hybrid Data Pipeline technology to access data in the cloud or on-premises behind a firewall. In one example, a partner is exposing standard SQL/REST from multiple data sources. Hybrid Data Pipeline’s new release allows them to leverage existing LDAP security while continuing to access data in many sources. Another partner scenario involves a financial company with strict data governance requirements managed via OAuth.
Support for external authentication in the latest Hybrid Data Pipeline release enables both of those companies to access their data with minimal security effort, as well as delivering compliance with federal standards.
Learn More
To learn more about the latest innovations in enterprise security, join our webinar on Enterprise Security in Data Access, or get started with Hybrid Data Pipeline today..
Join Security Webinar
Try Hybrid Data Pipeline

