How to Protect Your Data with Driver-Level Encryption

Progress DataDirect provides driver-level encryption, securing the last mile of connectivity with SSL/TLS Encryption.
When working with Big Data, security should be a priority. Several high-profile data breaches in government, retail and banking in the past few years have made this threat very real. In this new world where every detail of our lives can be recorded and held in databases, the organizations collecting that data have a responsibility to protect their customers. To do that, they need to stay ahead of the hackers and invest in technology that provides end-to-end encryption, even when data is temporarily stored in RAM where it is most vulnerable.
Data Breaches are Common in Healthcare
The healthcare industry is particularly vulnerable to security threats, with hundreds of intrusions reported every year, putting HIPAA-protected patient records at risk of being stolen. One of the biggest risks is when employees or contractors have access to non-encrypted patient records through their computer’s RAM. With patient records estimated to net 65 cents each on the black market (nearly twice as much as individual credit card records), this vulnerability presents a significant challenge to healthcare organizations around the world. In fact, one well-known recent security breach case occurred in 2013 at the U.S. Department of Veterans Affairs (VA), when approximately 4,000 patient records were stolen using an employee’s credentials.
In the United States, healthcare organizations must comply with HIPAA and are regulated by government agencies to prevent data theft. However, hackers are often able to outwit the most sophisticated safeguards
Hackers are making a living by adding plug-ins to computers that access residual data stored in RAM. They then turn around and sell that data or create fictitious claims to health insurance companies and government agencies to collect money.
How to Solve Security Risks with Driver-Level Encryption
So how do you stop hackers from gaining unauthorized access to critical data?
The best solution is to encrypt the connection between your database and application with a secure connector like those from Progress® DataDirect®. DataDirect provides driver-level encryption, securing the last mile of connectivity with SSL/TLS Encryption. This allows the client and server to send each other encrypted data that only they can decrypt.
DataDirect complies with PCI-DSS, SOX (Sarbanes Oxley) Section 404 and SOC 1 control objectives to help your company mitigate your security risk about ports and SSL connectivity.
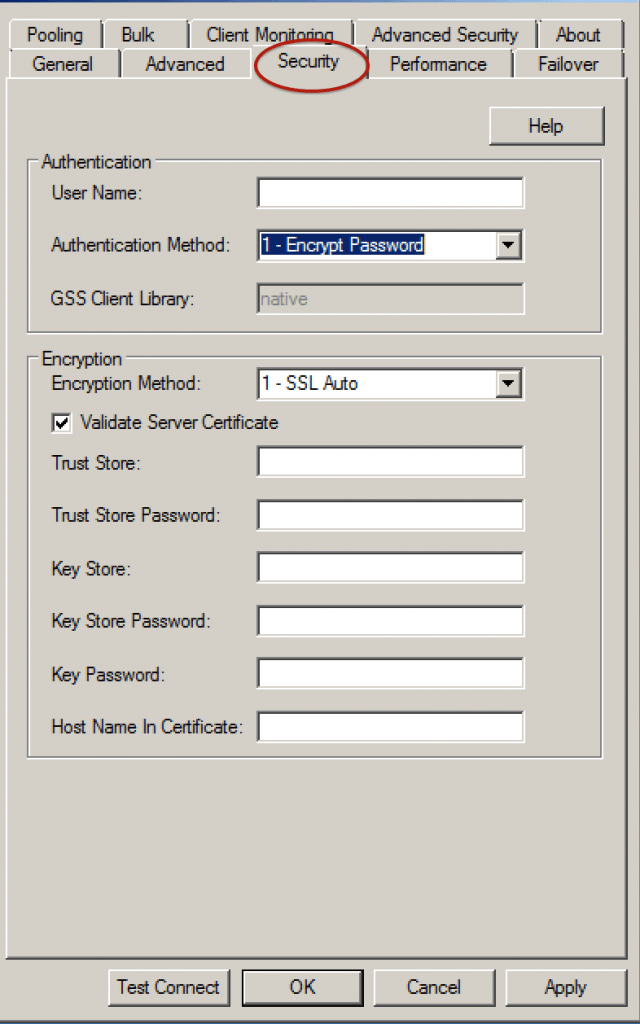
Figure 1: Progress DataDirect Connect for ODBC drivers support many popular encryption formats.
DataDirect Connect for ODBC drivers support many popular formats, including:
- DER Encoded Binary X.509
- Base64 Encoded X.509
- PKCS #12 / Personal Information Exchange
Here’s how it all works: When the client makes a connection request, the server presents its public certificate for the client to accept or deny. The client checks the issuer of the certificate against a list of trusted Certificate Authorities (CAs) that resides in an encrypted file on the client known as a trust store. If the certificate matches a trusted CA in the trust store, an encrypted connection is established between the client and server. If the certificate does not match, the connection fails and the driver generates an error.
Most trust stores are password-protected. The driver must be able to locate the trust store and unlock it with the appropriate password. Two connection string attributes are available to the driver to provide this information: “Trust Store” and “Trust Store Password”. The value of Trust Store is a pathname that specifies the location of the trust store file. The value of Trust Store Password is the password required to access the contents of the trust store.
DataDirect gives you the data connectivity solutions you require to encrypt your cached data from RAM memory in your company that help you diminish your vulnerability and comply with most PCI-DSS , SOX (Sarbanes Oxley) or SOC (Service Organization Controls) frameworks to avoid exposing data to non-employees in your organization.
Lock Down Your Data
Whether your critical data resides on an ATM machine in the banking sector or you are dealing with records in a healthcare or an e-commerce database, it is critical to encrypt your data and ensure it does not end up in the wrong hands.
At Progress, we want your data to be secure. For more information, don’t hesitate to leave a comment below or reach out to us. You can also grab a free trial and start reaping the benefits of end-to-end encryption right now.

