CASB vs. Security Gateways vs. Hybrid Data Pipeline

One interesting technology to grow out of IT disruption is the Cloud Access Security Broker. How does the CASB fit with Hybrid Data Pipeline?
Making Sense of Cloud to On-Premises Data Access
Disruption is like a wildfire to those unprepared—when it flares up there’s not much you can do, except watch it burn and pick up the pieces when it’s through. IT has been through a few wildfires lately. Cloud, mobile, citizen self-service, BYOD… Now they’re actively trying to piece things back together: determining which cloud applications to use, which employees are storing data in public services like Dropbox, integrating cloud and on-premises applications and data, and so forth.
The Cloud Access Security Broker
After a wildfire new life can flourish, and one of the interesting technologies to grow out of this array of disruption is the Cloud Access Security Broker (CASB)—not to be confused with your web proxy or security gateways. Increasingly, this is an area we get asked about, particularly in engagements connecting cloud applications to on-premises data through Hybrid Data Pipeline. Where do these three pieces fit? Does a CASB replace a security gateway? Is Hybrid Data Pipeline just a virtual CASB?
Salesforce Integration with On-Premises Data
One repeating use-case we see where this is an important topic involves Salesforce integration with on-premises data. Companies are trying to get more valuable, timely data in the hands of sales and support staff to help make better decisions. This is data that cannot simply be stored in the Salesforce platform, often due to regulatory issues or some inherent integration challenge. Most companies we encounter do not use a CASB today, nor is one required for a successful, secure deployment of Hybrid Data Pipeline. Since it is a popular topic however, I wanted to briefly touch on the role each plays in a successful cloud to on-premises data access strategy.
Three Primary Roles in Your Data Access Strategy
Security Gateway: Provide core firewall capabilities, IP and website filtering, protection against inbound threats. In short: protect me from the internet.
CASB: Discovery of cloud applications in use across the business, govern file/data transfers to unauthorized devices, enforce access rights and policies to various cloud applications. In short: provide context to the cloud apps I use and the devices that access them.
Hybrid Data Pipeline: RESTify on-premises databases, high performance access to on-premises data from the cloud, universal data API to accelerate bimodal IT initiatives.
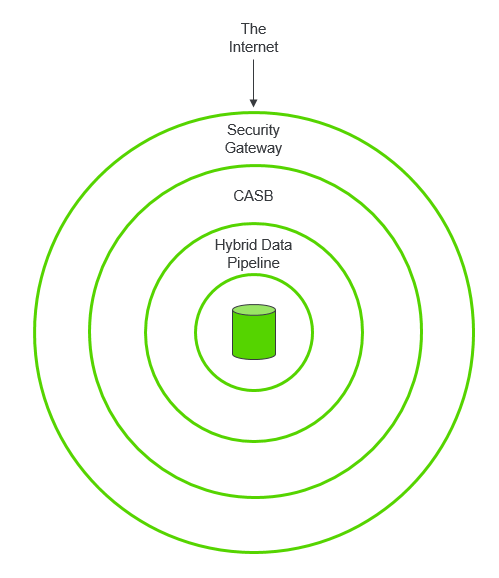
Figure 1: Network security for data access
Defense in Depth Approach to Secure Data Access
The answer to all the questions above then is: all three components handle an important task, and are thus very complimentary to one another. Together they can also provide a nice Defense in Depth approach to secure data access. It is best then to think of these components as concentric layers, with a security gateway at the outermost layer (closest to the internet), followed by a CASB and then Hybrid Data Pipeline (closest to the data).
Learn More About Hybrid Data Pipeline

