Secure Socket Layer (SSL) and Sitefinity

The content you're reading is getting on in years.
This post is on the older side and its content may be out of date.
Be sure to visit our blogs homepage for our latest news, updates and information.
In Symmetric Encryption, both parties encrypt and decrypt messages using the same cipher, which is only accessible using the same pubic key. To make the public key difficult to intercept, the two parties will share the public key over the phone or paper mail. Although this is the ideal encryption for the internet because it is the fastest way to encrypt data, anyone who intercepts the public key can encrypt and decrypt messages. Over the internet, it would be too slow to wait for a public key to be shared over the phone or through mail. To mend these flaws, many cryptologists will encrypt the public key asymmetrically and send it via the internet.
In asymmetric encryption, keys are generated in a private and public key pair. The public key is used as a unique identifier for each party. Messages can be created and sent using the public key, however, information can only be decrypted using the private key. As a result, the public keys are usually visible in encrypted communication. This is most obvious with assemblies from 3rd party vendors, such as Telerik, where you can easily see the public key by right clicking on the assembly, then selecting properties. In this encryption style, John Smith, for example, sends a message to Jane Jones using Jane’s public key because she is the only person who can decrypt it (provided that Jane has not shared its private key with anyone).
Many websites facilitate the transmission of personal information over the internet, so they implement a Secure Socket Layer (SSL) to encrypt the info from the client’s machine to the server and vice versa. SSL uses symmetric encryption for the messages and asymmetric encryption for the public key. One challenge with data encryption is verifying a party’s identity. At times, a user’s public key is susceptible to interception by another party and used in a man in the middle attack. In this case, someone intercepts messages from both parties, impersonates them, and send messages to each person. For more info on this attack, please read this article.
Another way to prove a user’s identity is a SSL certificate. When a user goes to a website, his or her computer communicates to a server with an IP address. Companies, such as Verisign, RapidSSL, and DigiCert, certify that the user’s computer is communicating to a certain IP address. This helps prevent fraud by ensuring that another server is not impersonating the website. If you are using a hosting provider, such as Discount ASP.NET, they will provide you with a public key and a unique IP. From there, you will take this info to a certificate authority and register for an SSL certificate. These expire after a year and they cost around $300 - $400 each, but longer periods of time can be purchased.
If your SSL is not set up properly, then you will get an error message saying that the website connect. It will look something like this:
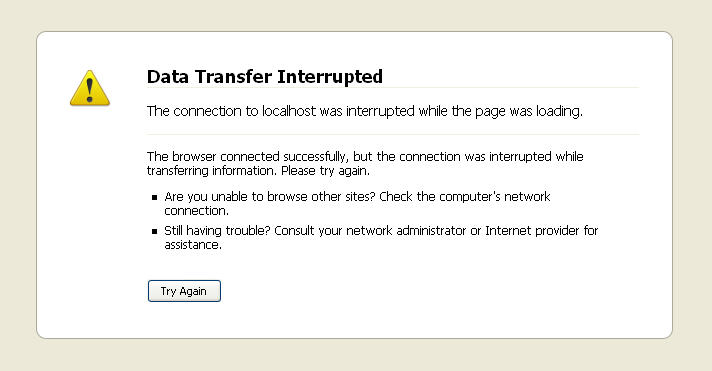
If you receive a message like this one, please check with your host to make sure that you have the SSL set up and your SSL provider that your certificate is valid.
After the SSL Certificate is set-up properly with the host, the developer must enable Sitefinity to use SSL. Although this would require code in a regular ASP.NET application, Sitefinity enables SSL by selecting the enable SSL property from the page properties section. This can be accessed by following these steps:
1. Login to the Sitefinity website
2. Click on pages
3. Select a page
4. Click on the properties tab
5. Scroll down and click on More Options
6. Next to Require SSL, click True
Out of the box, Sitefinity allows you to set a page property to enable SSL. For the admin, however, no out of the box solution exists. You can, however, add code to the login page’s code-behind to enable SSL for the admin as this forum post will demonstrate.
On some web pages, you will see a prompt informing you that some information is non-secure. This happens for two reasons. First, some content on the page could be from an absolute URI, such as http://www.mysite.com/picture.jpg. If the path is not absolute, then ASP.NET will replace the path with the rest of the website. Here are examples of non-absolute paths:
Rooted path:
/products/sitefinity.aspx
(always starts from the server root or immediately after the domain name )
Relative paths:
sitefinity/features.aspx
(the path starts from the current folder, in this case /products/)
Application based:
~/products/sitefinity.aspx
(this works only for server controls!!!)
Other than these paths, that prompt will also appear with any frame, iframe, or img tags with a blank or unspecified src attribute. Any use of "about:____" pages will also make that prompt appear. For a more detailed discussion, please read this article.
By having an enable SSL property on pages, Sitefinity makes it easier to encrypt information. This info must use relative URLs or be from another SSL page to be properly secured. Before this SSL feature can be used, you must ensure that your SSL certificate is set up properly on your server, or else the https: extension will not work on the pages.

