One of the main topics of this year’s HIMSS event was cybersecurity. It’s little wonder, and frankly about time. At every access point of every network within the healthcare industry, the fight for data security—and protecting the most private information of consumers—weighs heavy on the minds of those charged with its safekeeping.
Right now, hackers are tirelessly searching and probing for vulnerabilities in the networks of healthcare organizations of all sizes. Their objective is a simple one: to acquire the protected health information (PHI) of patients and consumers, which is worth 50X more than credit card information. Regulated by HIPAA to protect the privacy of individuals, and enforced by the OCR, the theft of PHI can jeopardize consumer—and the attacked entity’s—privacy, reputation and identity. Despite investments of billions of dollars on security—data theft and other forms of cyber crime continue to flourish, and often go undetected until it’s too late.
Hospitals Make Perfect Targets for Cyber Crime
According to Becker’s Hospital Review, 88% of all ransomware attacks are carried out against hospitals. Hospitals make perfect targets for these types of cyber attacks because they not only store sensitive information, but they also need immediate access to current patient information (e.g., treatment plans, medical histories) in order to deliver urgent care. Unavailability of patient records and information could lead to potentially catastrophic consequences for the patient. For some hospitals, not paying ransom demands is simply not an option. It’s do or die—literally.
Take the case of Hollywood Presbyterian Medical Center. In February 2016, the hospital was compelled to pay hackers $17,000 in Bitcoin to reclaim control of its own computer systems. Then, in May 2016, there was a cyber attack on Kansas Heart Hospital with the hackers extorting not one but two ransom payments to relinquish an illegal hold on the hospital’s data. In both of these cases, and in similar attacks waged on other healthcare institutions, the outcomes exposed a pervasive lack of readiness among hospitals and healthcare systems to successfully detect and repel cyber attacks and safeguard consumer data.
As a former Deputy Chief of Economic and Cyber Crime at the Philadelphia District Attorney’s Office, and Special Assistant U.S. Attorney, I’ve been investigating, prosecuting and thinking about data privacy, security, and cyber crime, particularly in healthcare for close to 20 years. But, these recent attacks make it clear that all of us in the industry must increase our vigilance as the attack methods used are evolving faster than most organizations’ abilities to protect their most critical information assets.
The High Cost of Cyber Attacks
Unfortunately, these increasingly common and opportunistic ransomware attacks are on the rise and will continue to adapt and grow in sophistication. Hackers will use the same AI that the industry is using to improve clinical outcomes, to improve their phishing emails. In fact, according to a recent analysis of 450 HIPAA incidents—either reported to the U.S Department of Health and Human Services or disclosed in the media—2016 was a record year for HIPAA data compliance breaches. And, with so much at stake in terms of damage to consumer confidence, brand integrity, and financial liability—cybersecurity and the protection of consumer information is not a problem for another day. You can’t afford to deal with it later.
Is your business ready for the worst? Don’t let data security become “do or die” for your organization.
With consumer data under constant threat, careful consideration of data security is more critical than ever. Naturally, as the risk of cyber attacks increase so too does the spending on security measures designed to combat them. In fact, according to Gartner, “By 2018, more than half of organizations will use security services firms that specialize in data protection, security risk management, and security infrastructure management to enhance their security postures.” Further, worldwide security spending is expected to reach $170 billion by 2020.
What You Can Do to Protect Your Data
You can prevent your organization from falling prey to the mercy of hackers by building a data-centered security strategy that includes the following components:
Advanced Data Security
Many databases have all-or-none data access, which is not sufficient to protect against modern cyber threats. Today, healthcare organizations need to define who can see what data at the most granular level. Exposure of PHI, even to valid application users, may violate privacy regulations and put consumer data at unnecessary risk. Controlling data access at the database-level eliminates these risks and prevents exploitation of application or network flaws that may disclose sensitive data.
An Enterprise NoSQL database platform not only helps healthcare organizations improve time to value by 6x (see infographic), but with MarkLogic 9, organizations will also find reassurance in knowing that they’re securing their highly confidential information on the only data platform ready to meet the evolving cybersecurity requirements of the modern enterprise (e.g., cloud). With security features that carefully manage how data is protected and exported, MarkLogic 9 will enable organizations to safeguard consumer privacy with capabilities such as:
- Advanced encryption that protects data from hackers and insider threats using standards-based cryptography, advanced key management, and granular separation of duties.
- Redaction features that eliminate exposure of sensitive information by removing specifics, or replacing it, to prevent sensitive data leaks.
- Element-level security. This allows specific information to be hidden from particular users, providing an even more granular level of security.
Master Data Management
A consistent and accurate view of your data is critical to decision-making. However, when data is spread across silos, it is difficult and costly to reconcile what the data means, whether it’s correct, how it relates to other data, and whether or not it’s secure. Master data management (MDM) can prove a challenging undertaking. The projects are commonly large and costly and can take years to execute—if they succeed at all. And most don’t. The main objective of master data management is to provide a single, unified source of truth. This will prevent users from using overlapping and possibly invalid or inconsistent versions of data. Without MDM, and among other problems, data silos and duplicate copies of data make it nearly impossible to secure and track the use of your data—increasing the possibility of breaches and exposure of sensitive consumer information.
Federation and warehousing with relational technology have proven too costly and brittle to solve these master data problems at scale. To protect its consumers, hospitals and health systems need a better approach to MDM (see video).
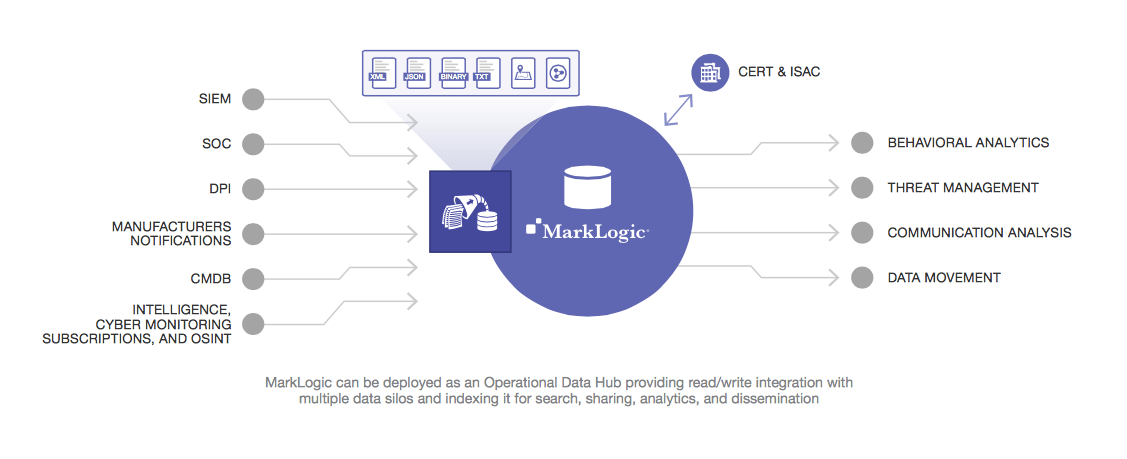
Operational Data Hub
With its data-centric enterprise architecture, building an operational data hub (ODH) will help healthcare organizations better protect their consumer information. An ODH enables you to bring all of your data together regardless of format, structure or schema. It provides the ability to index all structured and unstructured data and securely (and selectively) expose this information for search, data matching, alerting, and exploration. The ODH architecture brings applications to the data, instead of requiring you to copy data between applications. Further, an ODH solution developed on an Enterprise NoSQL database platform—with its inherent enterprise reliability and government-grade security—reduces application development time without sacrificing data governance, and provides a stable platform for evolving a master data management strategy.
Secure the Future of Your Business
Defense and intelligence agencies, large investment banks, and major healthcare organizations trust MarkLogic to ensure the data needed to run their most critical systems is accessible, governed and secured. That trust is well placed. With its granular access controls, data segmentation, and advanced encryption, the MarkLogic database platform has the security features healthcare institutions need to prevent their organizations and consumers from becoming the next victims of ransomware and other cyber attacks.

Bill Fox
Bill Fox JD, MA is the VP of Vertical Strategy and the Global CSO of Healthcare and Life Sciences at MarkLogic. He is a former attorney and healthcare executive with 25 years of experience and is a nationally recognized thought leader in healthcare predictive analytics, big data, program integrity and data security and privacy.
Bill serves on the HIMSS Health Business Solutions Taskforce and Business Edge Magazine, the thought leaders panel of Predictive Modeling News, and the Board of Directors of the Medical Identity Fraud Alliance.
He is a prior appointee to the Strategic Planning Committee of the National Healthcare Anti-Fraud Association and is a former Senior Fellow at the Jefferson School of Population Health. He has held healthcare leadership positions at Emdeon, Booz Allen Hamilton, and LexisNexis. He is the former Deputy Chief of Economic and Cyber Crime at the Philadelphia District Attorney's Office, Special Assistant United States Attorney for the Eastern District of Pennsylvania and law firm partner. Bill is a graduate of Temple University Graduate School and the Villanova School of Law.