SSL offloading
PREREQUISITES: SSL offloading sends the process of encoding and decoding SSL requests to a separate device. Therefore, you must:
- Acquire an SSL certificate from an authorized vendor, install, and configure it.
- Have an additional SSL offloading device that is specifically designed to perform SSL acceleration and termination.
SSL offloading moves SSL encoding and decoding functions away from busy webservers to specialized devices that are better equipped to handle CPU-intensive SSL calculations.
This allows the webservers to dedicate important CPU resources to other application processing tasks, which can improve performance.
RECOMMENDATION:
We recommend using SSL offloading only in case you have a lot of HTTPS requests.
NOTE: If you are using Network Load Balancing, the load balancer can perform this function. For more information, see Load balancing.
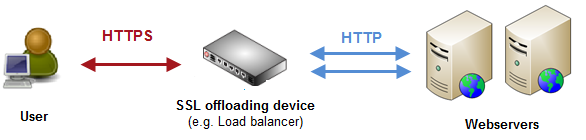
The following chart illustrates a setup with an SSL offloader:
Configure Sitefinity CMS to know that SSL requests will be offloaded:
- Navigate to Administration » Settings » Advanced » System » SSL Offloading.
- Select EnableSslOffloading.
- In HttpHeaderFieldName, enter the same HTTP header field name, as the one used by your SSL offloading device.
The reverse proxy (load balancer) communicates with a webserver using only unencrypted HTTP. Therefore, even if the request to the reverse proxy is encrypted HTTPS, you must specify the unencrypted HTTP header field name that will identify the originating protocol of the HTTP request.
The default value is X-Forwarded-Proto, which is the most commonly used by SSL offloading devices.
- In HttpHeaderFieldValue, leave the default value of https
The HTTPS header value indicates that the traffic from the client to the reverse proxy is encrypted. If you do not set this value or the abovementioned header, it will indicate that traffic from the client to the reverse proxy is not encrypted.
- Save your changes.
IMPORTANT: Your SSL offloading device must be set with the same HTTP header field name and HTTP value as the ones that you have entered in Sitefinity CMS. When the traffic must be encrypted between the reverse proxy and the client, before rerouting, the SSL offloading device must remove or replace any headers with above field name. Otherwise, a client can imitate the header field name and value with the malicious intent to present encrypted traffic as nonencrypted.