Split DNS solution when you use Sitefinity CMS as identity provider
Sitefinity CMS relies on OpenID Connect for authenticating users and allowing them to their profiles.
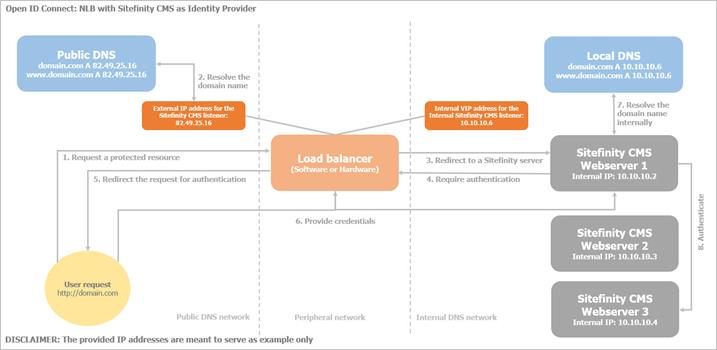
You can configure Sitefinity CMS in a load-balanced scenario, where the traffic goes through a load balancer (either software or hardware) or some other kind of network device for filtering traffic – reverse proxy, firewall, hygiene server, etc. In such case, if you use Sitefinity CMS as an identity provider, it is important that the servers, which participate in the load balancing, can resolve the site’s domain name, so that they can reach each other to complete the authentication process.
To accomplish this, you must configure an internal DNS. The local DNS has records of the internal IP addresses of the servers from the load balancing. This way, they are able to communicate with each other, without having to redirect the requests externally. If a server has to forward a request for authentication to the Sitefinity CMS STS, but cannot resolve the domain name internally, it will be forwarded to the load-balancer, treated as external, and blocked.
Process
When a request comes from the internet, the domain name (for example – domain.com) will point tо the public IP address on a listener of your load balancer. From there it will be routed to a Sitefinity CMS server. Then, it is important that the server can resolve the domain.com internally, as well. The most consistent and secure solution is to create an internal DNS record for your domain name to point to the load balancer. You must also make an additional configuration on your load-balanced solution to ensure that the load balancer listens on that internal IP address and routes the requests in a balanced way internally (within the internal network) to the Sitefinity CMS servers.
The following diagram displays how a request is routed until it is authenticated by the Sitefinity STS: